Port protection and restricting network access – Keeping the Data Safe – Securing a System
Port protection and restricting network access
Oracle Linux has a firewall built into the distribution. This firewall is called firewalld, short for firewall daemon. firewalld is a dynamic firewall management tool used on Linux systems that provides a simple and consistent way to manage firewall rules across different distributions. It is designed to allow administrators to manage firewall rules in a flexible and efficient way.
Getting ready
As with the other test, we will need an Oracle Linux system to play with. Nothing else is required. The system is enabled by default on most installations. To check the status of the daemon, you can use the systemctl command as follows:
systemctl status firewalld
The output is displayed in the following screenshot:
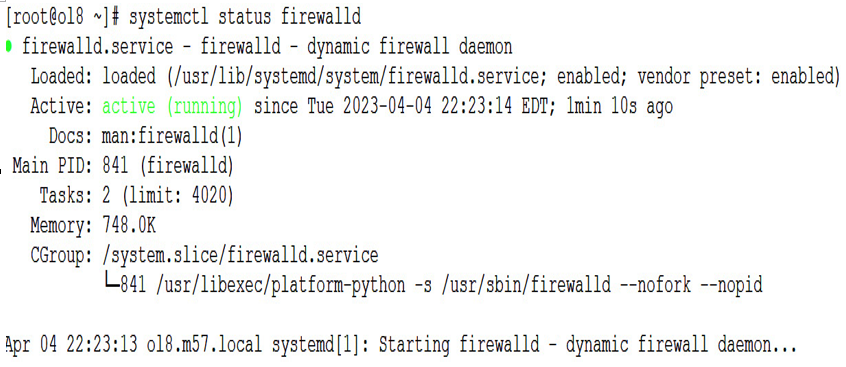
Figure 9.16 – firewalld status
How to do it…
You can see the current configuration using the firewall-cmd with the –list-all option:
[root@ol8 ~]# firewall-cmd –list-all
This will show the following information:
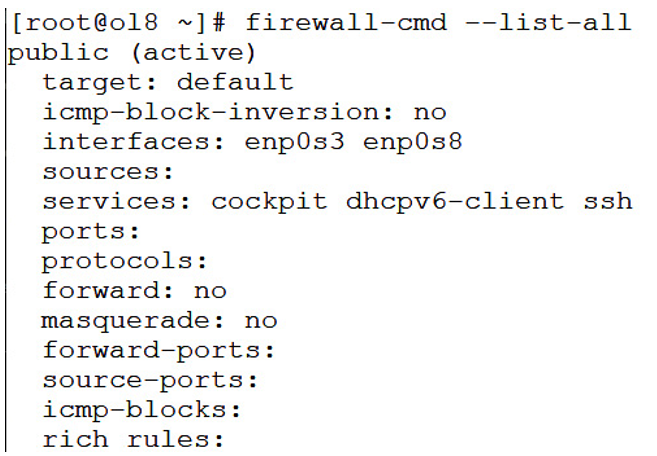
Figure 9.17 – firewall-cmd –list-all
The output of the preceding command displays a comprehensive summary of the active firewall rules and configurations managed by firewalld on a Linux system. The output is organized into several sections:
• public (active): This line displays the name of the active firewall zone, which in this example is the public zone. When Target:default is present, this indicates that this is the default zone and that it is currently active.
• interfaces: enp0s3 enp0s8: This line shows the network interface(s) that is assigned to the active firewall zone. In this example, both the enp0s3 and enp0s8 interfaces are assigned to the public zone.
• sources: This line displays the IP addresses or network ranges that are allowed to access the firewall zone. If no sources are defined, this line will be blank.
• services: cockpit dhcpv6-client ssh: This line lists the services that are allowed to access the firewall zone. In this example, incoming traffic for the cockpit, dhcpv6-client, and ssh services are allowed.
• ports: This line shows the TCP and UDP ports that are allowed to access the firewall zone. If no ports are defined, this line will be blank.
• protocols: This line shows protocols, such as TCP/UDP/ICMP, that are managed at a protocol level.
• forward: This shows whether zone forwarding is enabled.
• masquerade: no: This line indicates whether masquerading is enabled or disabled for the firewall zone. Masquerading allows packets from one network to appear as if they are coming from another network.
• forward-ports: This line shows any forwarded ports that are defined for the firewall zone. Forwarded ports allow incoming traffic on a specific port to be redirected to a different port or IP address.
• source-ports: This line shows any source ports that are defined for the firewall zone. Source ports allow incoming traffic from a specific port to be redirected to a different port or IP address.
• icmp-blocks: This line displays any Internet Control Message Protocol (ICMP) packets that are blocked by the firewall. ICMP packets are used for network diagnostics and troubleshooting.
• rich rules: This line shows any rich rules that are defined for the firewall zone. Rich rules allow more complex rules to be defined using a syntax that is similar to the iptables syntax.

