Validating adherence to a compliance policy 2 – Keeping the Data Safe – Securing a System
The families of profiles included are as follows:
- ANSSI-BP: ANSSI-BP is a set of security recommendations developed by the French National Agency for the Security of Information Systems (ANSSI) to provide guidance on securing information systems. The ANSSI-BP recommendations cover a wide range of topics, including network security, secure software development, access control, cryptography, incident response, and security monitoring.
- CJIS: The Criminal Justice Information Services (CJIS) are a division of the Federal Bureau of Investigation (FBI) in the United States. The CJIS division is responsible for providing law enforcement agencies with access to criminal justice information systems, which includes databases of criminal records, fingerprints, and other related information. The CJIS division was established in 1992 and provides services to more than 18,000 law enforcement agencies across the United States. Its mission is to provide accurate and timely information to law enforcement officials to help them solve and prevent crimes, while also ensuring the privacy and security of the information.
- NIST-800: NIST-800 refers to a series of guidelines and standards for information security developed by the National Institute of Standards and Technology (NIST) in the United States. The NIST-800 series includes a set of publications that provide guidance on various aspects of information security, such as risk management, security controls, and incident response. The NIST-800 series is widely used by government agencies, private sector organizations, and other entities to improve the security of their information systems. The publications in the series are regularly updated to reflect changes in the threat landscape and advancements in security technology.
- ACSC: The Australian Cyber Security Centre (ACSC) is a government agency that is responsible for enhancing the cyber security capabilities and resilience of the Australian government, businesses, and the community. The ACSC was established in 2014 and is a part of the Australian Signals Directorate (ASD).
- HIPAA: The Health Insurance Portability and Accountability Act (HIPAA) is a federal law in the United States that protects healthcare information. This law establishes standards for protecting the privacy and security of individuals’ health-related information. HIPAA includes specific requirements for securing electronic protected health information (ePHI), which is health information that is stored or transmitted electronically.
- PCS-DSS: The Payment Card Industry Data Security Standard (PCI-DSS) is a set of security standards established by major credit card companies that ensure that organizations that have access to credit card details protect the confidentiality and integrity of cardholder data. PCI-DSS is designed to reduce the risk of data breaches and credit card fraud.
- STIG: STIG stands for Security Technical Implementation Guide, which is a set of guidelines developed by the Defense Information Systems Agency (DISA) in the United States for securing information systems and software used by the Department of Defense (DoD). STIG provides detailed information on how to configure and maintain various technologies to meet DoD security requirements and ensure that systems are hardened against cyberattacks.
When picking a standard, you can use the default generic standards (such as the Standard System Security Profile for Oracle Linux 8 found at https://static.open-scap.org/ssg-guides/ssg-ol8-guide-standard.html) or a standard that aligns with the workload. For example, for healthcare, HIPAA is likely the appropriate standard. If you are in the US Federal Government ecosystem, the STIG standard is widely used even outside of the DoD. Once you pick the standard, you have several additional options, as seen in the following screenshot. You can pick a local or remote machine, as well as a remediation role. The remediation role allows the system to automatically resolve issues if possible, but any admin should be careful using this. This is because many of the standards can break system functionality. Always be careful when automatically remediating issues, especially with the more stringent standards, such as STIG and CJIS.
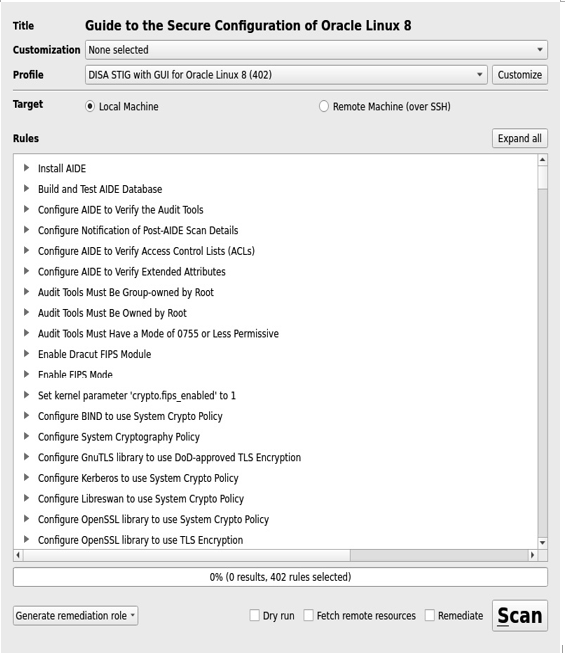
Figure 9.12 – Scan settings
Once you have made your choices, select Scan.
Depending on the standard used, the scan can run in as fast as a few seconds or take over 20 minutes. When the scan is complete, you can use the GUI to review the results:
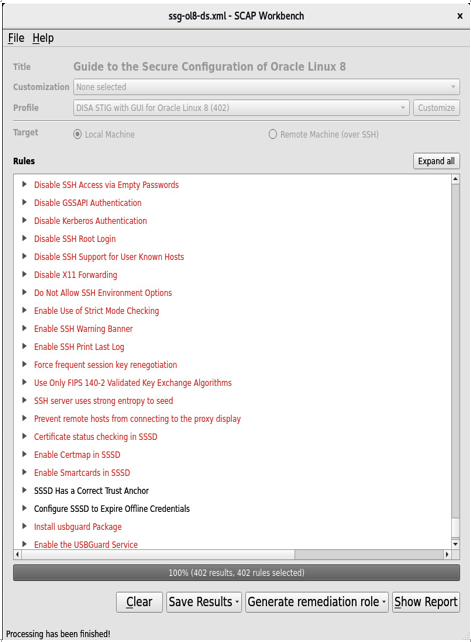
Figure 9.13 – Scan results
Not all fixes involve changing a simple setting. Some may require additional filesystems or kernel settings. To see the details of a finding, simply expand the results as seen in the following screenshot:
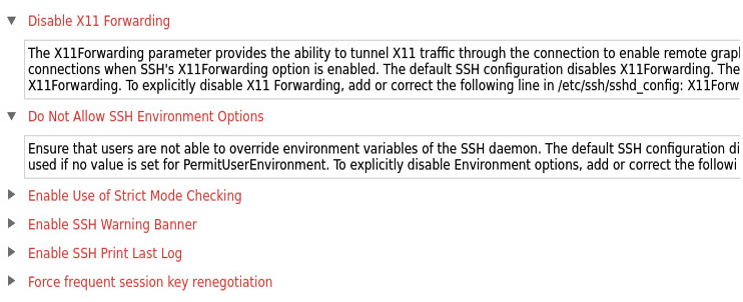
Figure 9.14 – Result details
At the bottom of the summary, you have several options:
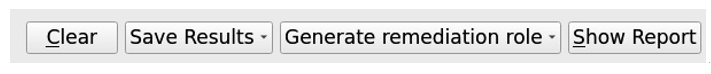
Figure 9.15 – Report options
These options are as follows:
- Save Results: Saves the results as a HTML file, an Asset Reporting File (ARF) file, or an Extensible Configuration Checklist Description Format (XCDDF) file
- Generate remediation role: Generates a script in bash, Ansible, or Puppet format to automate the remediation of the server
- Show Report: Opens up the HTML-formatted report in a browser


